Kaspersky Lab Cybersecurity Weekend Part 1: Shedding light on an invisible war
By Ryan Noik 2 May 2019 | Categories: Corporate Events
There is a large scale, mostly invisible war going on around the world. Do not look for tanks on the streets, soldiers on the ground or fighter jets in the sky. Much like the army of the dead in the most recent Game of Thrones episode, its attackers are often unseen until they are upon you, and they just keep coming.
This ‘army’ hides in computer systems, is potentially anywhere and no-one is invulnerable. At its Cybersecurity conference in Cape Town this week, Kaspersky Lab laid bare what is characterizing today’s cyber threat landscape, and even more importantly, what can be done to combat it now and in the future.
Like a fungus, but worse
The company began with a startling statistic – there are some 360 000 unique pieces of malware being released every single day.
Mohammad Amin Hasbini, the head of global research and analysis team for Middle East, Turkey and Africa (META), continued by giving some context to how cyberthreats have grown. “In 1994 we saw one new virus every hour, then in 2006 one new virus every minutes. By 2011, there was one new virus every second. As of today, in 2019, there are about three new viruses or malware being released every second,” he noted.
Sergey Novikov, the deputy director, global research and analysis team at Kaspersky Lab, explained that the threat landscape can be envisioned as a pyramid, that is divided into three layers. The bottom and largest layer accounts for 90% of traditional cybercrime, the middle most layer accounts for 9.9% of cyberattacks, which are targeted threats on organisations, and then the tip of the pyramid would be the 0.1% of cyberattacks, where cybercrime is used as a weapon to attack critical infrastructure like power plants and water facilities.
If the latter sounds like science fiction, or something out of a Die Hard movie, unfortunately it isn’t. Hasbini explained that those kinds of cyberattacks, which can destabilise a region, are more common than many suspect.

Sergey Novikov, the deputy director, global research and analysis team, Kaspersky Lab
A nation compromised
He elaborated that in the past the Ukraine, for example, had been targeted for a cyberattack and had its cities taken offline by cybercriminals, while other, undisclosed cities have had their water systems hacked and interrupted. Furthermore, sometimes attacks on nation states can be disguised by another, more common form of an attack. Hasbini cited one example where a country’s critical infrastructure was the victim of ransomware, but instead of the hijackers demanding payment as is usually expected, no contact was made, and it became clear that the intent was simply to disable the organisation in question.
Exacerbating the problem, he explained, is that governments don’t learn from other nation directed attacks, but instead wait until they become a target before reacting.
Mind your business
More common are attacks on organisations. Novikov warned that these kinds of cyber incidents are increasingly becoming larger, and thus much more important for organisations to take care of. Whereas the nation-state type attacks come from outside a country’s borders, much of the security compromisation in organisations comes from within, with many cyberattacks being caused by employees who inappropriately share files and resources.
Novikov continued that advanced persistent threats (APR) can be particularly difficult to detect, almost impossible to get rid of, and imbed themselves so deeply inside a company’s infrastructure that even if you do get rid of them, often times they come back again. Novikov explained that frequently these kinds of attacks infiltrate a system, gather information and seem to disappear only to come back again several months or even years later to do more damage.
Unfortunately, they are often allowed into a company’s network through spear phishing emails, with employees clicking on random links, whether on social networks, instant messages or email. In then, of course, there are infected USB flashdrives, which similarly can compromise an organisation’s network by uploading viruses.

Mohammad Amin Hasbini, the head of global research and analysis team for Middle East, Turkey and Africa
Cooperation among thieves
If that is not enough to curl your toes, then Hasbini’s note that cybercriminals often work together might. Indeed, some cybercriminals just concentrate on infiltrating and extracting data, including stolen digital identities, which is then sold on an underground online market, for other cybercriminals to exploit further.
Not at all unexpected is that mobile remains a problem as well, with smartphones and tablets growing in power and employees keeping sensitive data on the devices without adequate protection in place.
Everyone’s problem
Surely these kinds of attacks don’t affect South Africa directly, and it is more the developed nations that suffer the brunt of cybercrime, right? Wrong.
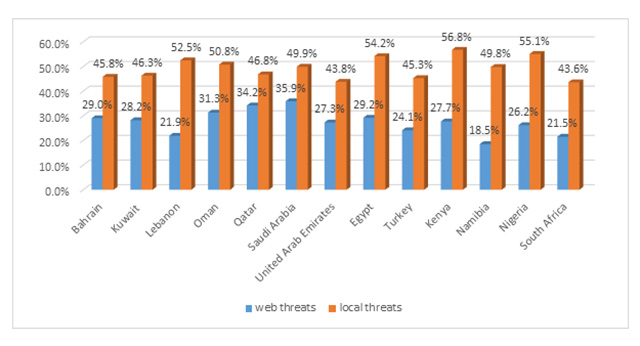
The company laid out just how prone Africa, along with the Middle East and Turkey actually is to malware and cybercrime.
Kaspersky Lab reported that there have been more than 150 million malware attacks in Q1 alone, representing an average of 1.6 million attacks per day, and an alarming 108% increase over Q1 2018. With some of the highest mobile phone penetration rates in the world, it should come as no surprise that the Middle East, Turkey and Africa (META) region also attracts a significant share of malware attacks targeted at mobiles. Mobile malware attacks in META in Q1 2019 numbered more than 368 000, an average of 4098 per day, and a spike of 118% when compared to Q1 2018.
Clearly cybersecurity is everyone’s concern now. The good news is that Kaspersky has a plan that it believes can help ensure that cybercrime can be mitigated, and the people and organisations in particular can do a better job at actively protecting themselves. That is revealed and unpacked, in a further installment.
Most Read Articles

Have Your Say
What new tech or developments are you most anticipating this year?



